HCP Terraform Enhancements: Cost Analytics, Notifications, and State Sharing
In recent months, HashiCorp has rolled out several key improvements to HCP Terraform and Terraform Enterprise, aimed at eliminating infrastructure blind spots and strengthening governance and security across the entire infrastructure lifecycle. These updates include general availability of billable resource analytics, project-level remote state sharing, module testing for dynamic credentials, and project-level notifications, along with the beta release of registry tagging. Below, we answer common questions about these features and how they can benefit your organization.
What is billable resource analytics and how does it improve cost management?
Billable resource analytics, now generally available in HCP Terraform, provides comprehensive visibility into resource consumption across your organization. Previously, organizations using resources under management (RUM)-based billing could only see total billable resources at the organization level, making it difficult to pinpoint where costs originated. The new feature breaks down current totals of billable managed resources by project and workspace, giving decision-makers the insights needed to identify high-consumption areas, reduce waste, and optimize infrastructure investments.
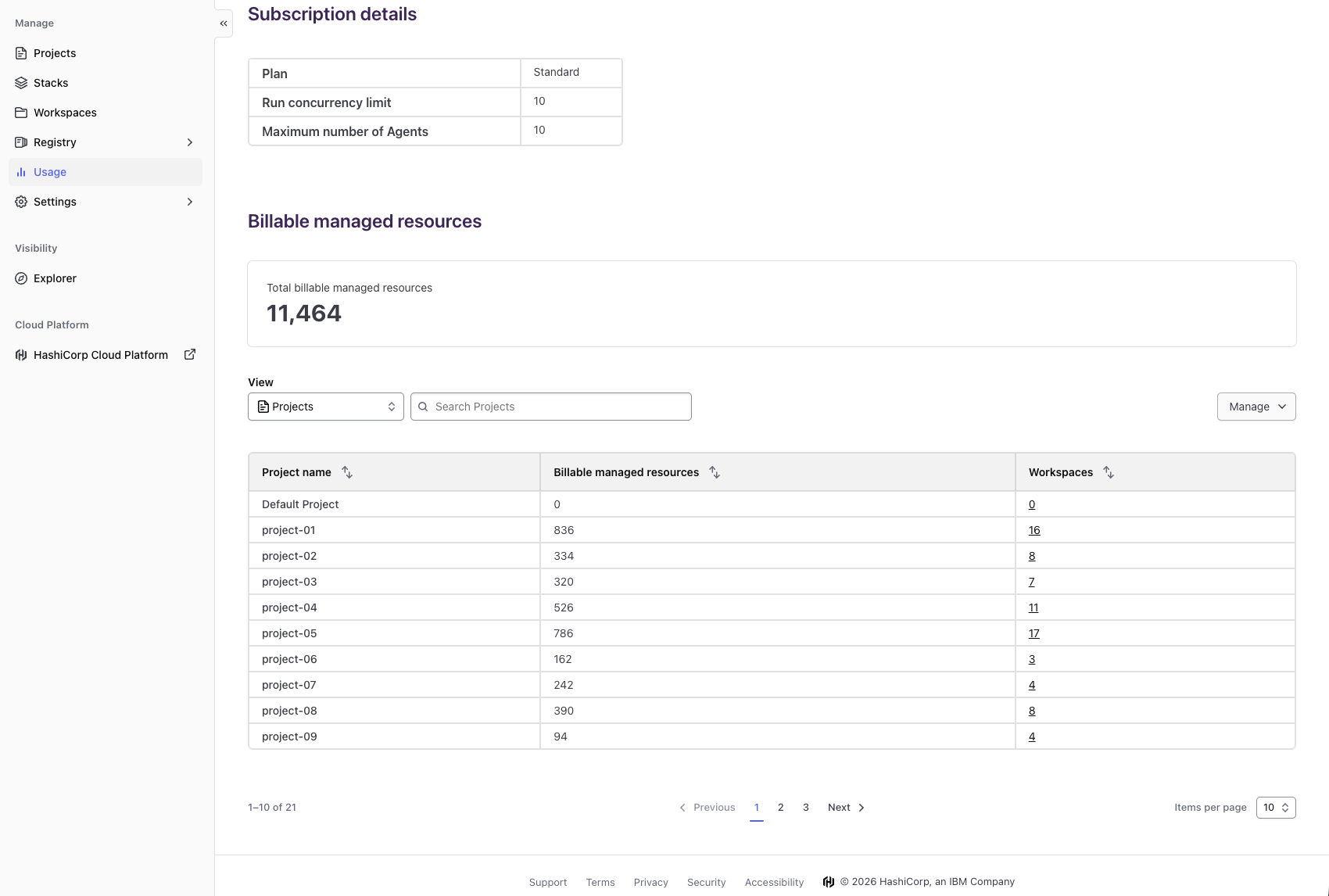
Available as a self-service view on the existing usage page, this capability allows any user on a paid HCP Terraform plan to access detailed cost data without delays. Benefits include cost visibility and predictability, enabling proactive management of spending, and data-driven decision making, allowing leaders to allocate resources strategically based on actual consumption patterns. By eliminating guesswork, organizations can stay within budget and align infrastructure costs with business priorities.
How does project-level remote state sharing work and what gap does it fill?
Project-level remote state sharing, now generally available for HCP Terraform and Terraform Enterprise, addresses a critical trade-off faced by platform teams managing large-scale infrastructure. Previously, sharing data between workspaces required custom, often fragile solutions or granting overly broad access. This new capability allows teams to share state data at the project level, enabling more granular control while maintaining security and consistency.
With project-level remote state sharing, administrators can define precise permissions for which workspaces within a project can access the state of other workspaces. This simplifies data exchange for dependencies, reduces configuration complexity, and eliminates the need for manual workarounds. The feature enhances collaboration across teams while preserving governance boundaries, making it easier to build composite architectures without compromising security. By closing this gap, HashiCorp enables more efficient and safe infrastructure management at scale.
What is module testing for dynamic credentials and why is it important?
Module testing for dynamic credentials is now generally available in HCP Terraform. This feature allows developers to test Terraform modules that use dynamic credentials—such as those provided by AWS, Azure, or GCP through the Terraform provider—without exposing static, long-lived secrets. During testing, modules can securely authenticate using ephemeral credentials that are automatically generated and scoped to the test environment.
This capability is crucial for maintaining security in CI/CD pipelines. Previously, testing modules that required cloud provider credentials often meant storing sensitive keys in code or insecure vaults, increasing the risk of leaks. With dynamic credentials, tests run in a sandboxed, temporary context that minimizes blast radius. Additionally, it simplifies testing workflows because credentials are managed by Terraform Cloud and do not require manual rotation. The result is faster, safer module development that encourages best practices in infrastructure as code.
How do project-level notifications improve governance?
Project-level notifications, now generally available in HCP Terraform and Terraform Enterprise, allow platform teams to set up alerts for specific events at the project scope—rather than only at the workspace or organization level. This enables more targeted governance, such as notifying a project owner when a run fails, when a state version is locked, or when resource limits are approached.
Previously, administrators had to either create workspace-level notifications for each workspace (which is time-consuming) or rely on organization-wide alerts that could be noisy and irrelevant. Project-level notifications strike a balance, giving teams the flexibility to define notification rules that apply to all workspaces within a project. For example, a team can receive a Slack message or email whenever a workspace in their project completes a destructive operation. This improves response times, ensures accountability, and reduces the risk of misconfiguration spreading across environments.
What is registry tagging and what benefits does it offer in beta?
Registry tagging, currently in beta for the Terraform Registry, introduces the ability to assign custom tags to modules. Tags can be used to categorize modules by attributes such as team ownership, compliance level, environment (e.g., dev, staging, prod), or lifecycle stage. This makes it easier for users to discover and filter relevant modules within their organization’s private registry.
The primary benefit is improved module discoverability and governance. Without tagging, users must rely on names or descriptions to find the right module, which can be ambiguous when many modules exist. Tags provide a flexible, searchable taxonomy. For example, a platform team can tag all modules that are SOC 2 compliant with “security-audited” and then enable CI checks to require that only tagged modules are used in production workspaces. As a beta feature, registry tagging is still evolving, but it promises to streamline module curation and adoption across large organizations.
How do these features collectively enhance infrastructure lifecycle management?
Collectively, the five new features—billable resource analytics, project-level remote state sharing, module testing for dynamic credentials, project-level notifications, and registry tagging—close significant gaps in the infrastructure lifecycle. Cost visibility enables financial accountability, state sharing reduces operational friction, dynamic credential testing strengthens security in development pipelines, project-level alerts improve incident response, and registry tagging simplifies module organization.
By addressing these areas, HashiCorp helps organizations move from reactive management to proactive governance. Platform teams gain better control over budgets, access, and security without needing custom scripts or third-party integrations. The features are designed to work together: for instance, cost analytics can trigger project-level notifications when spending passes a threshold, while registry tagging ensures only approved modules are used in workspaces that share state. This ecosystem reduces infrastructure blind spots and empowers teams to scale their cloud operations confidently and efficiently.
Related Articles
- Building and Testing Sealed Bootable Container Images for Fedora Atomic Desktops
- Major Security Patches Issued Across Linux Distributions: Urgent Updates Required
- 10 Major Linux Updates You Can't Miss This Month
- Alpine Linux Outage: Billing Issue Causes Temporary Service Interruption
- Comprehensive Guide to This Week's Critical Security Patches Across Major Linux Distributions
- Boosting Linux Per-Core I/O Performance: A Developer's Guide
- 10 Crucial Insights Into Kconfirm: Revolutionizing Linux Kernel Configuration
- Hacktivist Group Claims Responsibility for Widespread Ubuntu Service Disruptions